
March 17, 2026
The Developer’s Guide to Secure Job Hunting in 2026
The Industrialization of Recruitment Fraud
The IBM Cost of a Data Breach 2025 Report confirms a notable shift in the global landscape. For the first time in five years, the global average cost of a data breach has decreased, falling to 4.44 million USD from the 2024 record high of 4.88 million USD. The decrease in total cost is a result of improved corporate defenses, yet the frequency of phishing (16%) and the high cost of malicious insider attacks (4.92 million USD) demonstrate that human-centric vectors remain the most expensive to manage.
The impact on the job market is significant. Federal Trade Commission (FTC) data shows that job-related fraud losses reached 752 million USD in the first nine months of 2025, nearly surpassing the total for all of 2024 (763.5 million USD), and significantly exceeds the 501.4 million USD lost in 2023.
Generative AI allows attackers to craft convincing, personalized outreach in five minutes - a task that previously required 16 hours of manual effort for group of experts. Today, 16% of breaches involve AI-driven tactics, with AI-generated phishing (37%) and deepfake impersonation (35%) leading the way (IBM Cost of Data Breach 2025).
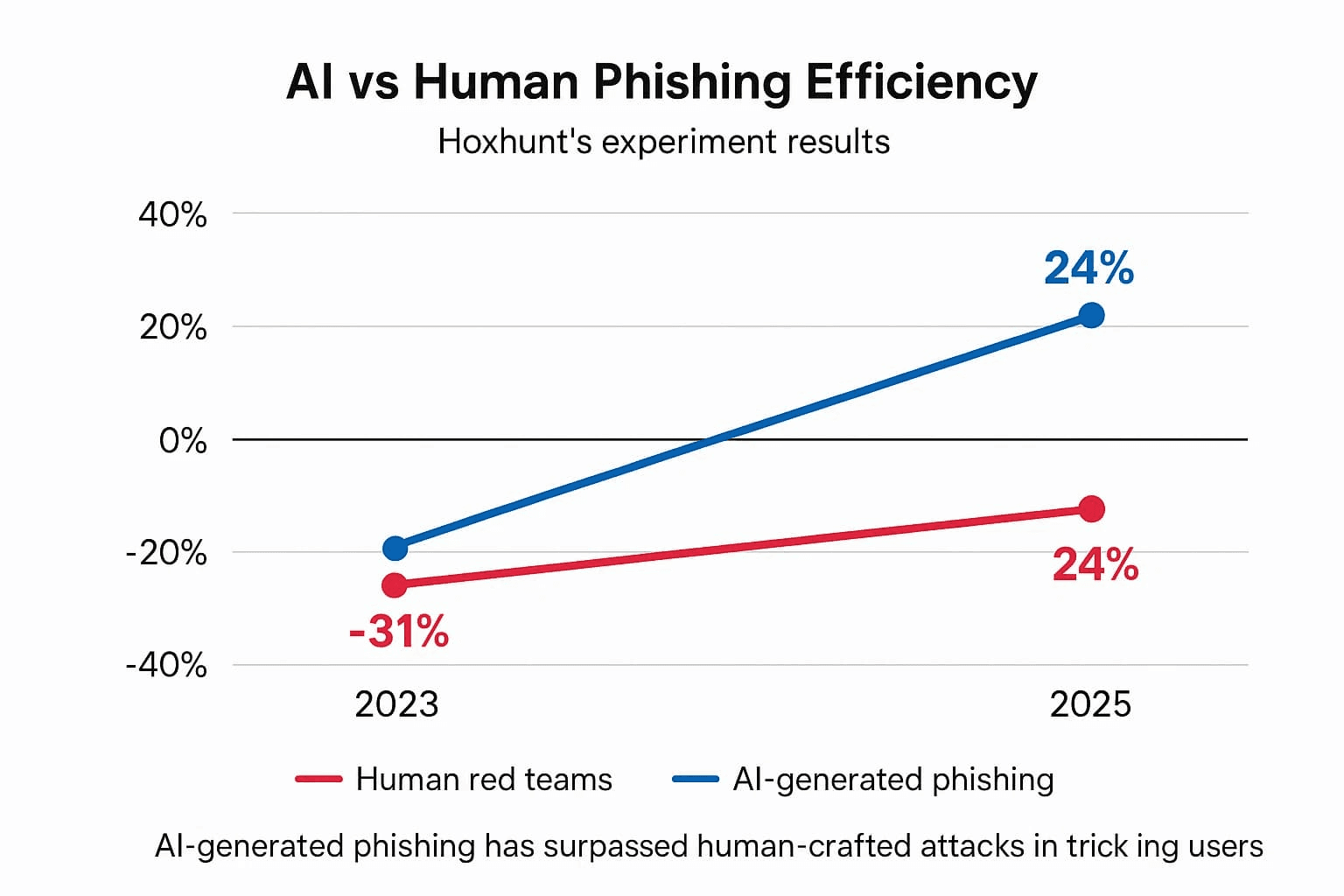
Source: deepstrike
Attackers now utilize "high-touch" operations that mimic legitimate hiring stages to deceive even senior technical professionals, not only easy-to-spot phishing scenarios.
The Erosion of Traditional Red Flags: From Clumsy Scams to Agentic AI Operations
I would say, “historically”, identifying a job scam was a matter of basic pattern recognition. You looked for the "too good to be true" offer, the broken English or the suspicious request for a WhatsApp/Telegram move within the first three messages.
These legacy scams generally focused on immediate financial theft through advance fee fraud (request for e.g. onboarding fees or equipment insurance), identity harvesting (early requests for SSNs or ID photos before an interview) or domain mismatch (outreach from e.g. @gmail.com instead of @company.com)
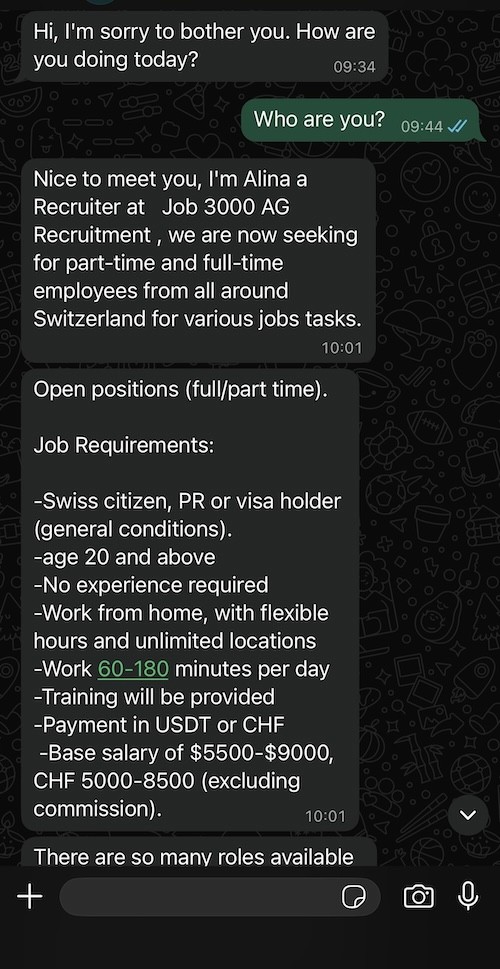
Example of a classic recruitment scam message received in Switzerland via Whatsapp
However, as of early 2026, these indicators have become largely obsolete. Recent data from Anthropic confirms a shift toward "Agentic AI" operations, where attackers deploy almost autonomous, multi-persona AI teams. In PwC 2026 Global Digital Trust Insights Agentic AI is ranked among the "top security capabilities" that organizations plan to prioritize in 2026 for defense because it is already being used on offense.
These agents could also manage an end-to-end recruitment funnel - including flawless written communication, active LinkedIn networking and multi-stage technical coordination. This evolution means that the absence of grammatical errors or the presence of a professional-looking profile is no longer a certificate of legitimacy.
Scammers are investing time into "high-touch" interactions to secure much more valuable targets: corporate access, intellectual property or long-term identity theft.
Identifying "Basic" Recruitment Spam
Category | Red Flag Indicator | Legitimate Industry Standard |
|---|---|---|
Financials | Requests for "onboarding fees," equipment deposits, or check-cashing. | No legitimate employer or agency requests money from a candidate. |
Communication | Messages via WhatsApp/Telegram from unknown numbers or generic | Professional outreach via LinkedIn or verified corporate email domains (e.g., |
Urgency | Aggressive pressure to sign a contract or "secure a spot" within hours. | Hiring processes for senior roles typically take weeks and involve multiple stakeholders. |
Personal Data | Requests for SSN, passport scans, or bank details before a video interview. | Sensitive data is only collected after a formal offer and through secure HR portals. |
Language | Frequent syntax errors, poor grammar, or generic greetings (e.g., "Dear Job Seeker"). | High-quality, personalized outreach reflecting an understanding of your specific stack/history. |
Hardware | Instructions to buy your own laptop with a promise of reimbursement. | Companies provide managed hardware or use specific procurement systems for remote staff. |
The Offer | Compensation that is significantly above the market rate for "minimal effort." | Compensation is aligned with local market benchmarks and technical seniority. |
The "Zero-Trust" Interview: Defending Against Contagious Malware
The 2026 threat landscape has moved beyond simple phishing. We are now seeing advanced campaigns - sophisticated, multi-stage operations that weaponize the technical assessment phase. For a developer, the risk is big. It is the total compromise of your local environment.
To understand the scale of these operations, consider these campaigns documented in the last years:
The CrowdStrike “CRM” Lure (January 2025)
In this campaign, attackers created a replica of the CrowdStrike hiring process. Candidates for "Junior Developer" roles were directed to a spoofed corporate site and instructed to download an "Employee CRM application" to "streamline" their interview.
The app was a downloader for the XMRig cryptominer, which executed in the background while displaying a fake "Installation Failed" error to the user. The malware performed environment checks for virtualization and debugging tools, only executing if it determined it was on a "real" (non-sandboxed) machine.
More information available here.
Contagious Interview Campaign (2022 - ongoing)
In this operation, attackers used "high-fidelity" social engineering to mimic a standard long-term hiring process. After building rapport, candidates were sent a technical task containing the BeaverTail infostealer and OtterCookie malware. The initial payload harvested passwords from browser keychains, scraped .env files for cloud credentials, and drained cryptocurrency wallet extensions.
Once the environment was compromised, it deployed InvisibleFerret, a Python-based backdoor that provided the attackers with full remote control, keystroke logging, and the ability to exfiltrate sensitive intellectual property from the developer's machine.
More information available here.
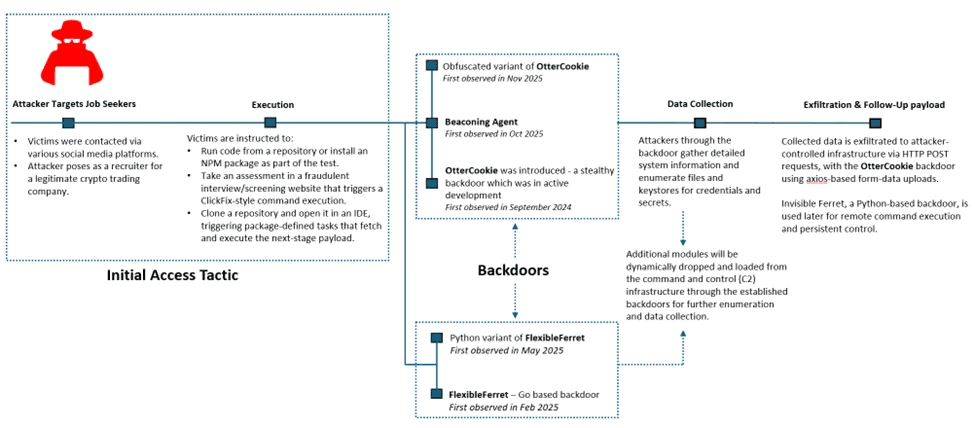
Attack chain overview presented by Microsoft Researchers
Attacker group, sponsored by North Korea have targeted at least 3,136 individual IP addresses and 20 major organizations globally.
Jamf Threat Labs said it detected LinkedIn personas potentially associated with PurpleBravo that masqueraded as developers and recruiters and claimed to be from the Ukrainian city of Odesa, along with several malicious GitHub repositories that are designed to deliver known malware families like BeaverTail.
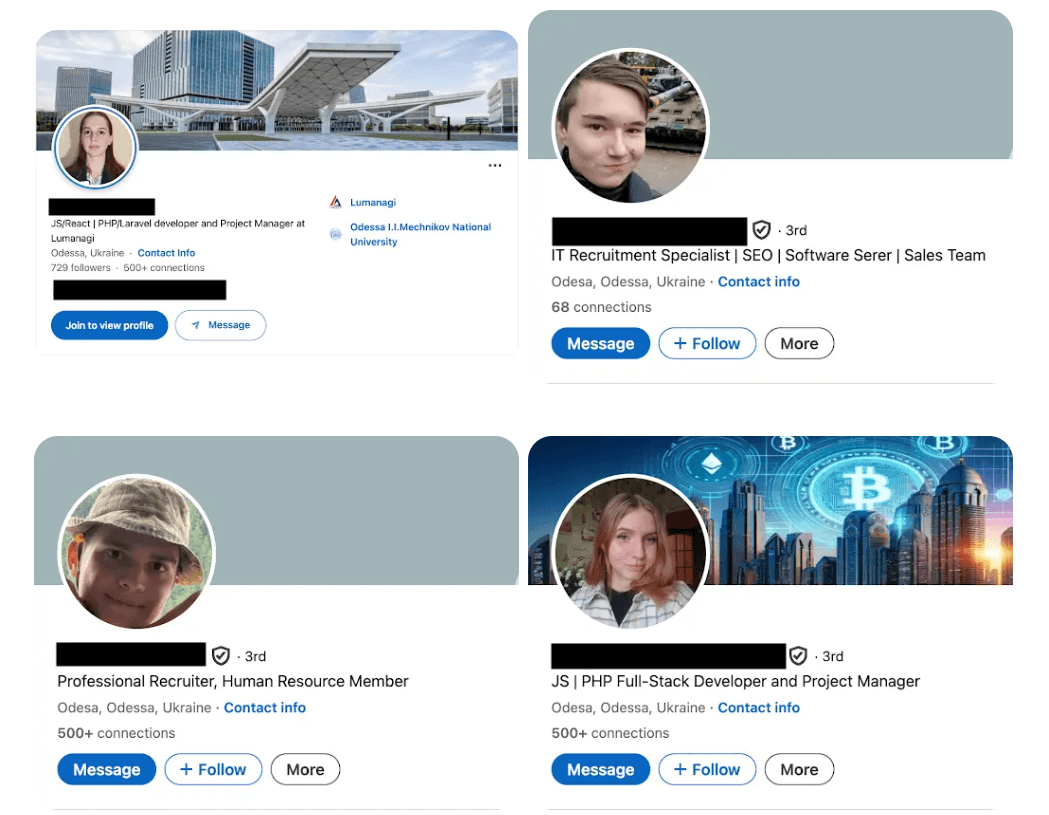
LinkedIn profiles associated with the PurpleBravo, source: hackernews
On the surface, a developer or recruiter from Odesa reaching out in 2026 feels entirely plausible. Since 2022, the Ukrainian tech workforce has become globally distributed and heavily reliant on remote freelance opportunities, making unsolicited LinkedIn outreach from this region seem routine.
There is often a subconscious desire to support professionals from conflict zones, which can lead a candidate to be more "helpful" and less critical of a non-standard hiring process.
Many of these LinkedIn personas are built on "aged" accounts - either stolen or cultivated over years - with real endorsements and mutual connections in the European tech scene.
The "Zero-Trust" Interview
Since the mechanics of these scams are discovered, the focus must shift from awareness to active defense. Standard security hygiene is no longer sufficient when the "recruiter" on the other side is a scammer supported by AI tooling, designed to exploit the very tools you use for work.
Start with one principle: treat interview code as untrusted until proven safe.
Red Flags: Recognition and Immediate Action
Pillar I Identity & Social Engineering
Signal in the Interview | The Objective | Your First Move |
|---|---|---|
The "Sunk Cost" Application | To build psychological investment via a 20+ question form, making you more likely to ignore later red flags. | Decline tasks that require excessive unpaid labor before a human interview. |
Real-Time Face Swap | To validate a stolen or synthetic identity of a high-level executive during a video call. | Ask the interviewer to turn their head sideways or hold up a specific number of fingers. Request a quick identity check via a official company email or ask a question only a local (e.g., Zurich-specific) would know. |
High-Volume Outreach | To create a "surround sound" effect of legitimacy across LinkedIn, Upwork, and Freelancer. | Cross-reference the company's official website and verified corporate email domains. |
Seasoned Breached Profiles | To bypass "New Account" flags by using aged, stolen credentials from established recruiters. | Perform a historical audit of the profile for sudden shifts in activity or posting style. |
Pillar 2: Technical Execution & Environment
Signal in the Interview | The Objective | Your First Move |
|---|---|---|
The ClickFix "Camera Fix" | To trick you into running a terminal command that installs BeaverTail or WeaselStore. | Never execute terminal commands provided by a website to fix browser hardware issues. |
"Run This Script" Pressure | To achieve immediate execution on your primary, non-sandboxed device during the call. | Move all interview-related execution to a disposable, air-gapped VM or container. |
The "TsunamiKit" Installer | To deploy RATs that monitor your clipboard and keystrokes via a fake .NET performance tool. | Reject any "helper" binaries. Professional assessments do not require custom hardware installers. |
Tailwind/Vite Config Ghost | To trigger a malicious | Audit the |
Pillar 3: Repository & Code Integrity
Signal in the Interview | The Objective | Your First Move |
|---|---|---|
Low-History GitHub Org | To utilize "throwaway" infrastructure that can be deleted once the malware is delivered. | Inspect the provenance, contributors, and creation dates of the organization before cloning. |
Obfuscated Code/Binaries | To hide malicious payloads or logic bombs within legitimate-looking project files. | Request raw source code and refuse to run pre-compiled blobs or minified scripts. |
Repo Write-Access Request | To facilitate privilege escalation or allow the attacker to exfiltrate your private work. | Keep all repository access read-only and use a secondary, non-primary Git profile. |
Malicious .zip Attachments | To deliver the initial payload directly, bypassing the transparency of a public Git host. | Insist on a public repository link and scan all incoming documents for macro-based threats. |
Pillar 4: Operational & Contractual
Signal in the Interview | The Objective | Your First Move |
|---|---|---|
Crypto-Only / No NDA | To avoid the "paper trail" of traditional banking systems and legal accountability. | Pause the process and demand formal corporate documentation and IBAN-based payment terms. |
Urgent Platform Shift | To move the conversation away from monitored channels like LinkedIn to unlogged apps like Telegram. | Maintain all professional communication on trackable, officially sanctioned corporate channels. |
The "Ghost" Interviewer | To hide the fact that you are interacting with an AI or a proxy who cannot speak the language fluently. | Insist on at least one synchronous, live video interaction before handling proprietary code. |
Execution Pressure | To force a mistake by creating a false sense of urgency or a "limited time" opportunity. | Maintain a standard 24-hour review period for any technical task or contractual document. |
Sources: based on eset, cybertex.io and attack.mitre
The New Rules
The shift in the 2026 recruitment landscape is definitive. We have moved past the era where a "professional-looking" LinkedIn profile served as a certificate of legitimacy. To successfully search for a job in this environment, we should embrace a security-first philosophy that treats every interaction as a high-stakes verification exercise.
Treat every unexpected message on LinkedIn or GitHub as a potential test of your security, not just an interest in your resume. Assume the person on the other side might be after your data rather than your talent.
Never run interview code on your main computer. Always use a "disposable" digital workspace that isn't connected to your personal/company files or passwords.
Implement a two-channel verification rule. If a recruiter reaches out on one platform, verify their identity through an independent corporate channel before sharing any technical data.
Do not fear the loss of "speed" in your hiring process. Legitimate, high-value firms will respect - and often mirror - your commitment to security and rigorous due diligence.
The scammer traps of 2026 only succeed when they exploit our desire to be helpful, efficient and trusting. In a world of AI-generated fakes, your best tool is your own common sense. Stay cautious, stay “isolated” and stay safe :).
Ready to build your technical team with greater precision?
We help startups, scaleups, and enterprises reduce avoidable hiring costs and reallocate time and capital toward product, performance, and growth. Let’s discuss how placementist can bring scientific rigor to your technical hiring.
Photo: Pixabay x Nanobanana
The Industrialization of Recruitment Fraud
The IBM Cost of a Data Breach 2025 Report confirms a notable shift in the global landscape. For the first time in five years, the global average cost of a data breach has decreased, falling to 4.44 million USD from the 2024 record high of 4.88 million USD. The decrease in total cost is a result of improved corporate defenses, yet the frequency of phishing (16%) and the high cost of malicious insider attacks (4.92 million USD) demonstrate that human-centric vectors remain the most expensive to manage.
The impact on the job market is significant. Federal Trade Commission (FTC) data shows that job-related fraud losses reached 752 million USD in the first nine months of 2025, nearly surpassing the total for all of 2024 (763.5 million USD), and significantly exceeds the 501.4 million USD lost in 2023.
Generative AI allows attackers to craft convincing, personalized outreach in five minutes - a task that previously required 16 hours of manual effort for group of experts. Today, 16% of breaches involve AI-driven tactics, with AI-generated phishing (37%) and deepfake impersonation (35%) leading the way (IBM Cost of Data Breach 2025).
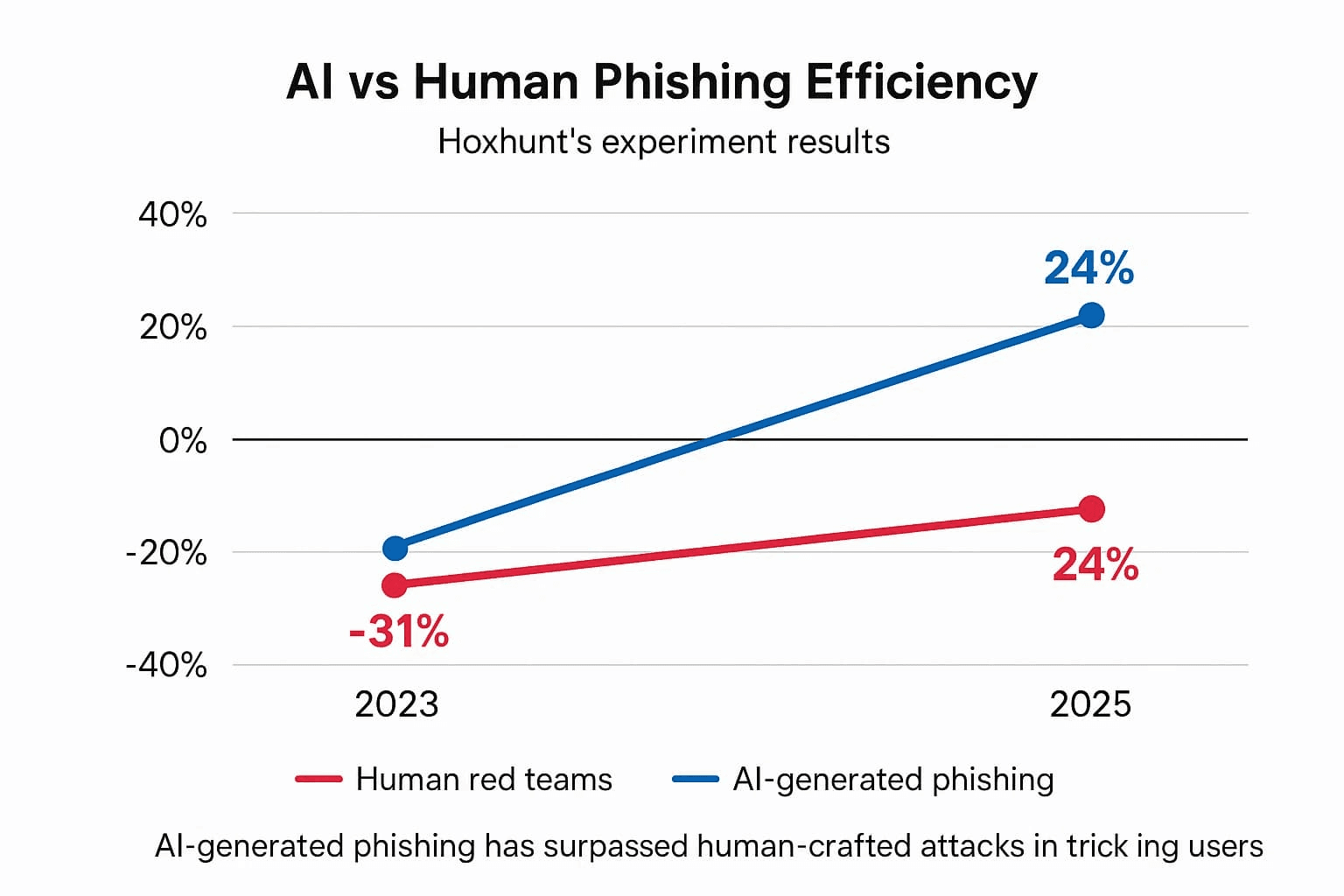
Source: deepstrike
Attackers now utilize "high-touch" operations that mimic legitimate hiring stages to deceive even senior technical professionals, not only easy-to-spot phishing scenarios.
The Erosion of Traditional Red Flags: From Clumsy Scams to Agentic AI Operations
I would say, “historically”, identifying a job scam was a matter of basic pattern recognition. You looked for the "too good to be true" offer, the broken English or the suspicious request for a WhatsApp/Telegram move within the first three messages.
These legacy scams generally focused on immediate financial theft through advance fee fraud (request for e.g. onboarding fees or equipment insurance), identity harvesting (early requests for SSNs or ID photos before an interview) or domain mismatch (outreach from e.g. @gmail.com instead of @company.com)
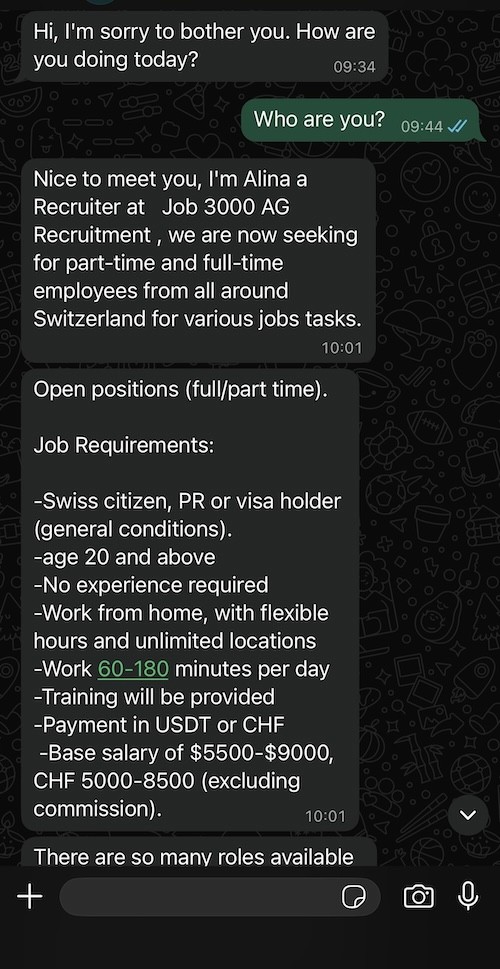
Example of a classic recruitment scam message received in Switzerland via Whatsapp
However, as of early 2026, these indicators have become largely obsolete. Recent data from Anthropic confirms a shift toward "Agentic AI" operations, where attackers deploy almost autonomous, multi-persona AI teams. In PwC 2026 Global Digital Trust Insights Agentic AI is ranked among the "top security capabilities" that organizations plan to prioritize in 2026 for defense because it is already being used on offense.
These agents could also manage an end-to-end recruitment funnel - including flawless written communication, active LinkedIn networking and multi-stage technical coordination. This evolution means that the absence of grammatical errors or the presence of a professional-looking profile is no longer a certificate of legitimacy.
Scammers are investing time into "high-touch" interactions to secure much more valuable targets: corporate access, intellectual property or long-term identity theft.
Identifying "Basic" Recruitment Spam
Category | Red Flag Indicator | Legitimate Industry Standard |
|---|---|---|
Financials | Requests for "onboarding fees," equipment deposits, or check-cashing. | No legitimate employer or agency requests money from a candidate. |
Communication | Messages via WhatsApp/Telegram from unknown numbers or generic | Professional outreach via LinkedIn or verified corporate email domains (e.g., |
Urgency | Aggressive pressure to sign a contract or "secure a spot" within hours. | Hiring processes for senior roles typically take weeks and involve multiple stakeholders. |
Personal Data | Requests for SSN, passport scans, or bank details before a video interview. | Sensitive data is only collected after a formal offer and through secure HR portals. |
Language | Frequent syntax errors, poor grammar, or generic greetings (e.g., "Dear Job Seeker"). | High-quality, personalized outreach reflecting an understanding of your specific stack/history. |
Hardware | Instructions to buy your own laptop with a promise of reimbursement. | Companies provide managed hardware or use specific procurement systems for remote staff. |
The Offer | Compensation that is significantly above the market rate for "minimal effort." | Compensation is aligned with local market benchmarks and technical seniority. |
The "Zero-Trust" Interview: Defending Against Contagious Malware
The 2026 threat landscape has moved beyond simple phishing. We are now seeing advanced campaigns - sophisticated, multi-stage operations that weaponize the technical assessment phase. For a developer, the risk is big. It is the total compromise of your local environment.
To understand the scale of these operations, consider these campaigns documented in the last years:
The CrowdStrike “CRM” Lure (January 2025)
In this campaign, attackers created a replica of the CrowdStrike hiring process. Candidates for "Junior Developer" roles were directed to a spoofed corporate site and instructed to download an "Employee CRM application" to "streamline" their interview.
The app was a downloader for the XMRig cryptominer, which executed in the background while displaying a fake "Installation Failed" error to the user. The malware performed environment checks for virtualization and debugging tools, only executing if it determined it was on a "real" (non-sandboxed) machine.
More information available here.
Contagious Interview Campaign (2022 - ongoing)
In this operation, attackers used "high-fidelity" social engineering to mimic a standard long-term hiring process. After building rapport, candidates were sent a technical task containing the BeaverTail infostealer and OtterCookie malware. The initial payload harvested passwords from browser keychains, scraped .env files for cloud credentials, and drained cryptocurrency wallet extensions.
Once the environment was compromised, it deployed InvisibleFerret, a Python-based backdoor that provided the attackers with full remote control, keystroke logging, and the ability to exfiltrate sensitive intellectual property from the developer's machine.
More information available here.
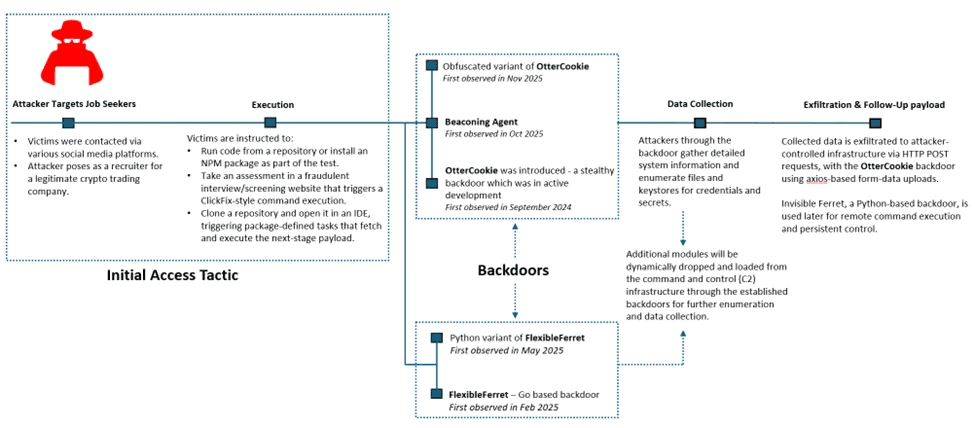
Attack chain overview presented by Microsoft Researchers
Attacker group, sponsored by North Korea have targeted at least 3,136 individual IP addresses and 20 major organizations globally.
Jamf Threat Labs said it detected LinkedIn personas potentially associated with PurpleBravo that masqueraded as developers and recruiters and claimed to be from the Ukrainian city of Odesa, along with several malicious GitHub repositories that are designed to deliver known malware families like BeaverTail.
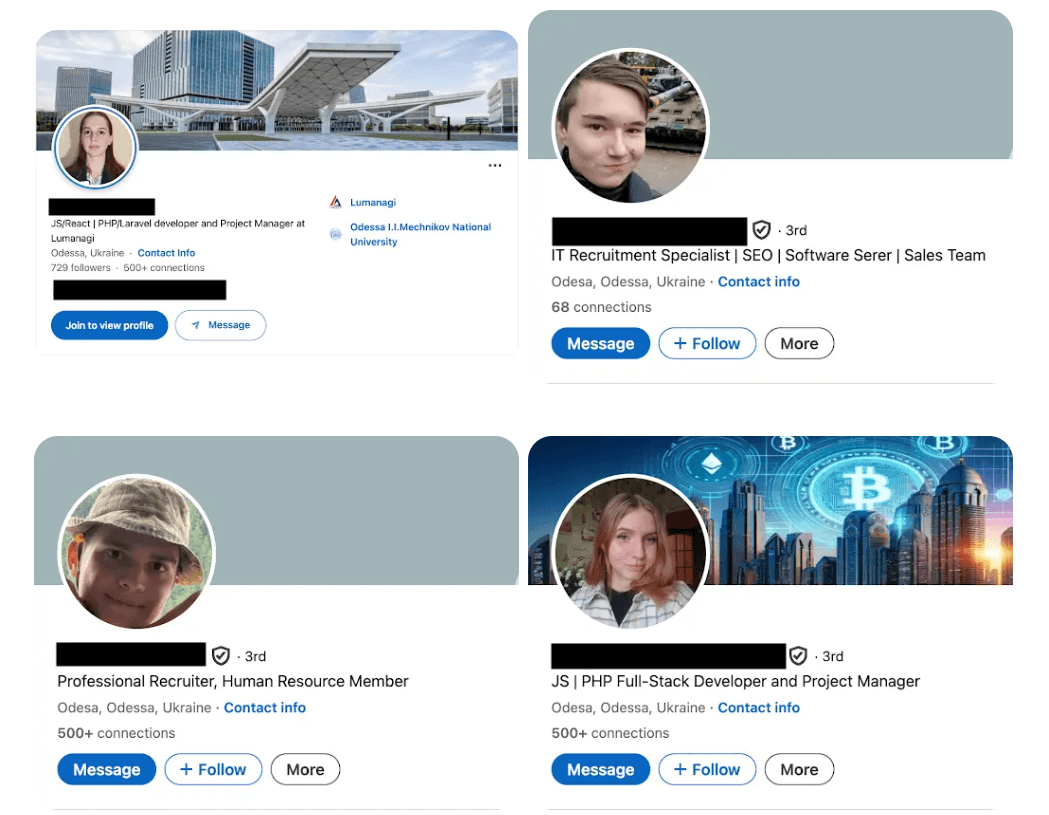
LinkedIn profiles associated with the PurpleBravo, source: hackernews
On the surface, a developer or recruiter from Odesa reaching out in 2026 feels entirely plausible. Since 2022, the Ukrainian tech workforce has become globally distributed and heavily reliant on remote freelance opportunities, making unsolicited LinkedIn outreach from this region seem routine.
There is often a subconscious desire to support professionals from conflict zones, which can lead a candidate to be more "helpful" and less critical of a non-standard hiring process.
Many of these LinkedIn personas are built on "aged" accounts - either stolen or cultivated over years - with real endorsements and mutual connections in the European tech scene.
The "Zero-Trust" Interview
Since the mechanics of these scams are discovered, the focus must shift from awareness to active defense. Standard security hygiene is no longer sufficient when the "recruiter" on the other side is a scammer supported by AI tooling, designed to exploit the very tools you use for work.
Start with one principle: treat interview code as untrusted until proven safe.
Red Flags: Recognition and Immediate Action
Pillar I Identity & Social Engineering
Signal in the Interview | The Objective | Your First Move |
|---|---|---|
The "Sunk Cost" Application | To build psychological investment via a 20+ question form, making you more likely to ignore later red flags. | Decline tasks that require excessive unpaid labor before a human interview. |
Real-Time Face Swap | To validate a stolen or synthetic identity of a high-level executive during a video call. | Ask the interviewer to turn their head sideways or hold up a specific number of fingers. Request a quick identity check via a official company email or ask a question only a local (e.g., Zurich-specific) would know. |
High-Volume Outreach | To create a "surround sound" effect of legitimacy across LinkedIn, Upwork, and Freelancer. | Cross-reference the company's official website and verified corporate email domains. |
Seasoned Breached Profiles | To bypass "New Account" flags by using aged, stolen credentials from established recruiters. | Perform a historical audit of the profile for sudden shifts in activity or posting style. |
Pillar 2: Technical Execution & Environment
Signal in the Interview | The Objective | Your First Move |
|---|---|---|
The ClickFix "Camera Fix" | To trick you into running a terminal command that installs BeaverTail or WeaselStore. | Never execute terminal commands provided by a website to fix browser hardware issues. |
"Run This Script" Pressure | To achieve immediate execution on your primary, non-sandboxed device during the call. | Move all interview-related execution to a disposable, air-gapped VM or container. |
The "TsunamiKit" Installer | To deploy RATs that monitor your clipboard and keystrokes via a fake .NET performance tool. | Reject any "helper" binaries. Professional assessments do not require custom hardware installers. |
Tailwind/Vite Config Ghost | To trigger a malicious | Audit the |
Pillar 3: Repository & Code Integrity
Signal in the Interview | The Objective | Your First Move |
|---|---|---|
Low-History GitHub Org | To utilize "throwaway" infrastructure that can be deleted once the malware is delivered. | Inspect the provenance, contributors, and creation dates of the organization before cloning. |
Obfuscated Code/Binaries | To hide malicious payloads or logic bombs within legitimate-looking project files. | Request raw source code and refuse to run pre-compiled blobs or minified scripts. |
Repo Write-Access Request | To facilitate privilege escalation or allow the attacker to exfiltrate your private work. | Keep all repository access read-only and use a secondary, non-primary Git profile. |
Malicious .zip Attachments | To deliver the initial payload directly, bypassing the transparency of a public Git host. | Insist on a public repository link and scan all incoming documents for macro-based threats. |
Pillar 4: Operational & Contractual
Signal in the Interview | The Objective | Your First Move |
|---|---|---|
Crypto-Only / No NDA | To avoid the "paper trail" of traditional banking systems and legal accountability. | Pause the process and demand formal corporate documentation and IBAN-based payment terms. |
Urgent Platform Shift | To move the conversation away from monitored channels like LinkedIn to unlogged apps like Telegram. | Maintain all professional communication on trackable, officially sanctioned corporate channels. |
The "Ghost" Interviewer | To hide the fact that you are interacting with an AI or a proxy who cannot speak the language fluently. | Insist on at least one synchronous, live video interaction before handling proprietary code. |
Execution Pressure | To force a mistake by creating a false sense of urgency or a "limited time" opportunity. | Maintain a standard 24-hour review period for any technical task or contractual document. |
Sources: based on eset, cybertex.io and attack.mitre
The New Rules
The shift in the 2026 recruitment landscape is definitive. We have moved past the era where a "professional-looking" LinkedIn profile served as a certificate of legitimacy. To successfully search for a job in this environment, we should embrace a security-first philosophy that treats every interaction as a high-stakes verification exercise.
Treat every unexpected message on LinkedIn or GitHub as a potential test of your security, not just an interest in your resume. Assume the person on the other side might be after your data rather than your talent.
Never run interview code on your main computer. Always use a "disposable" digital workspace that isn't connected to your personal/company files or passwords.
Implement a two-channel verification rule. If a recruiter reaches out on one platform, verify their identity through an independent corporate channel before sharing any technical data.
Do not fear the loss of "speed" in your hiring process. Legitimate, high-value firms will respect - and often mirror - your commitment to security and rigorous due diligence.
The scammer traps of 2026 only succeed when they exploit our desire to be helpful, efficient and trusting. In a world of AI-generated fakes, your best tool is your own common sense. Stay cautious, stay “isolated” and stay safe :).
Ready to build your technical team with greater precision?
We help startups, scaleups, and enterprises reduce avoidable hiring costs and reallocate time and capital toward product, performance, and growth. Let’s discuss how placementist can bring scientific rigor to your technical hiring.
Photo: Pixabay x Nanobanana
Latest Articles

February 26, 2026
The Business Benefits of Evidence-Based Hiring

February 26, 2026
The Business Benefits of Evidence-Based Hiring
March 11, 2026
The Evidence-Based Guide to Candidate Attraction
March 11, 2026
The Evidence-Based Guide to Candidate Attraction

March 17, 2026
The Developer’s Guide to Secure Job Hunting in 2026

March 17, 2026
The Developer’s Guide to Secure Job Hunting in 2026
Ready to build your technical team?
Let's discuss your hiring needs and how evidence-based recruitment might help
Ready to build your technical team?
Let's discuss your hiring needs and how evidence-based recruitment might help
Ready to build your technical team?
Let's discuss your hiring needs and how evidence-based recruitment
might help.
Ready to build your technical team?
Let's discuss your hiring needs and how evidence-based recruitment might help
Quick links
Quick links
Quick links
Quick links

